Supporting Audits with VIVA#
Audits are the reports required for a potential certification according to ISO 27001 based on IT-Grundschutz. With the add-on VIVA, audits can be created and managed. In addition to audits, VIVA provides further reports for continuous quality assurance.
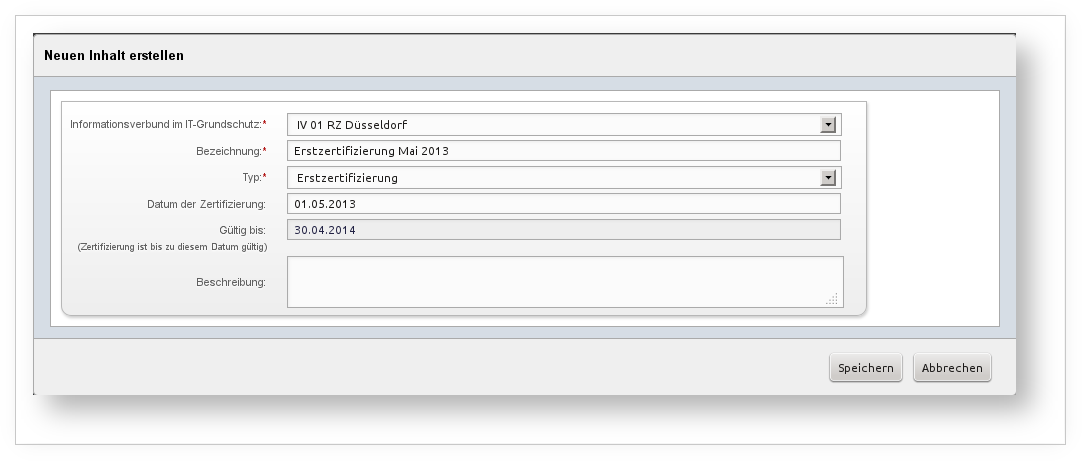
Creating audits#
Once all information has been gathered and documented within VIVA, audits can be created. These are based on the selected information domain and the type of certification being pursued (initial certification, surveillance audit, etc.). In terms of content and formatting, they follow the requirements specified in the BSI standards. Audits can be found under the corresponding item in the menu tree.
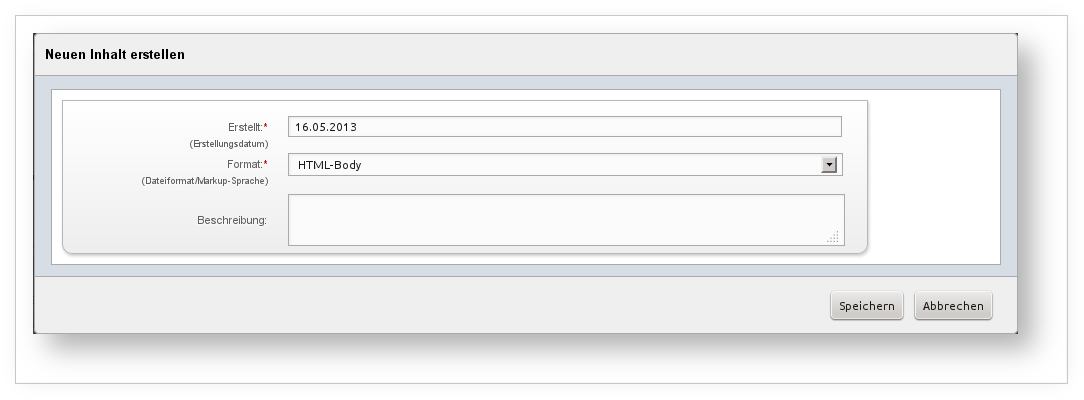
The following output formats are available for selection:
- HTML (including head section and stylesheet)
- HTML body (without head section and stylesheet)
The generated HTML documents contain all information needed to further process them in other applications. They can easily be imported into a word processor and adapted to your own requirements (for example, to match the corporate design).
Reference documents#
The following section covers the individual reference documents.
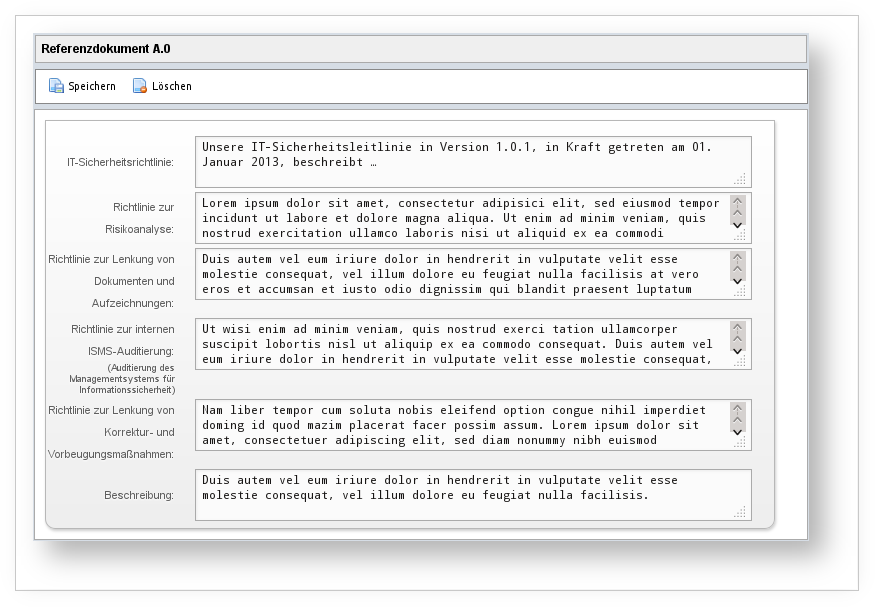
Reference document A.0 IT Security Policies#
The first reference document contains several overarching specifications that can be documented directly in the respective audit.
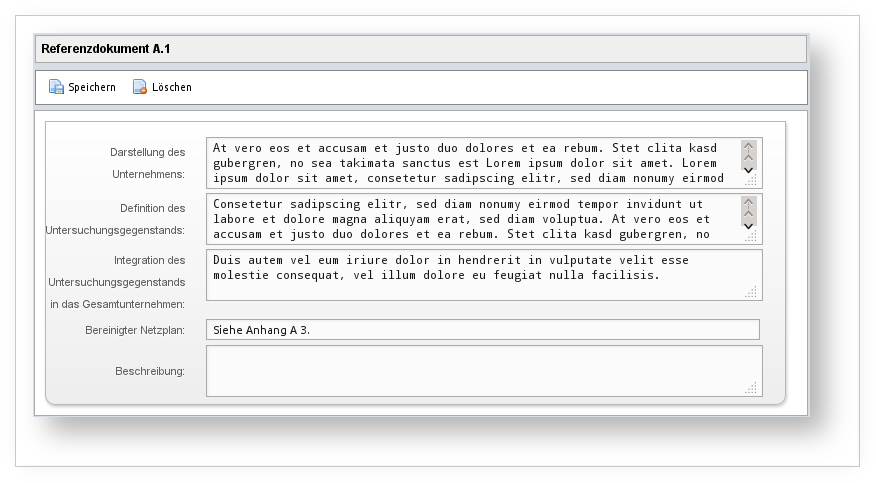
Reference document A.1 IT Structural Analysis#
The second reference document draws partly from data documented within the selected information domain (see Creating target groups and Assigning target objects), and partly from additional data that can be entered directly in the respective audit.
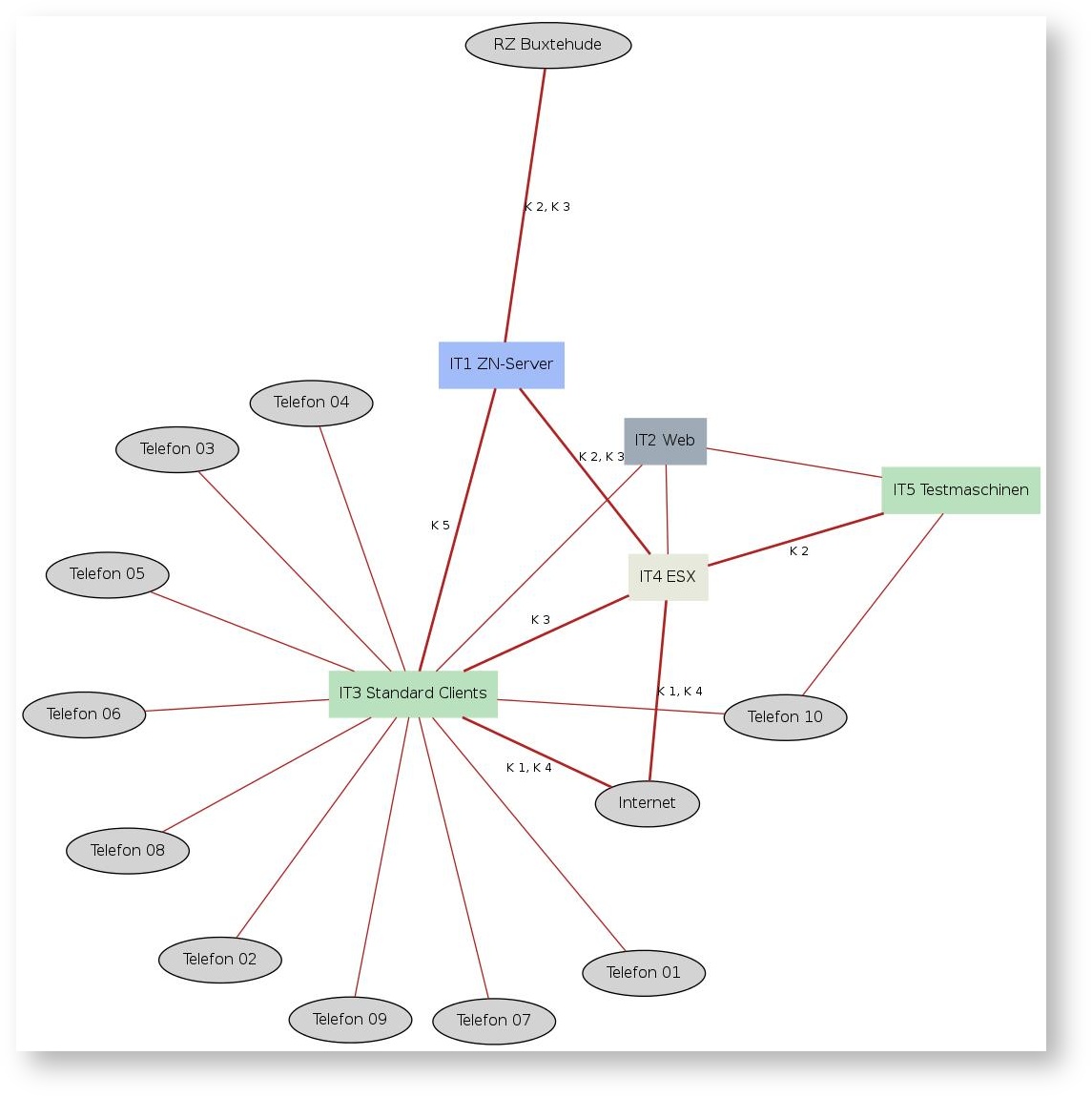
The reference document includes, among other things, a cleaned network plan (see BSI standard 100-2, chapters 4.2.3 and 4.3.5). This can either be referenced textually via the corresponding form field, or -- if the field is left empty -- an automatically generated diagram representing the network plan is used. The generated image contains all information required for a cleaned network plan that is available through the current documentation: this includes the individual target groups, their communication links to each other, and the associated criticalities. This is supplemented by a color scheme based on the object type configuration, using the target objects assigned to the target groups.
Please observe the optional system requirements.
Reference document A.2 Protection Needs Assessment#
This reference document contains only data that has already been documented within the selected information domain. See Defining protection needs categories and Determining protection needs.
Reference document A.3 Modeling of the Information Domain#
This reference document contains only data that has already been documented within the selected information domain. See Modeling information domains.
Reference document A.4 Results of the Baseline Security Check#
This reference document contains only data that has already been documented within the selected information domain. See Implementing measures.
Reference document A.5 Supplementary Security Analysis#
This reference document contains only data that has already been documented within the selected information domain. See Performing supplementary security analysis.
Reference document A.6 Risk Analysis#
This reference document compiles information to cover a risk analysis according to BSI standard 100-3. See Risk analysis based on IT-Grundschutz.
Reference document A.7 Risk Treatment Plan#
This reference document is not yet generated at this time.