Workflow with VIVA#
The possibilities of IT documentation are already diverse in i-doit and can be adapted to the requirements and needs of the respective organizational environment. The add-on VIVA is no exception: even though the underlying IT-Grundschutz standards impose many requirements, they are open to interpretation in numerous places. VIVA attempts to accommodate this. Nevertheless, certain work sequences have become established in practice, and they are described in more detail in this chapter. This example claims neither completeness nor binding authority. Additional intermediate steps such as adapting the documentation are likely necessary.
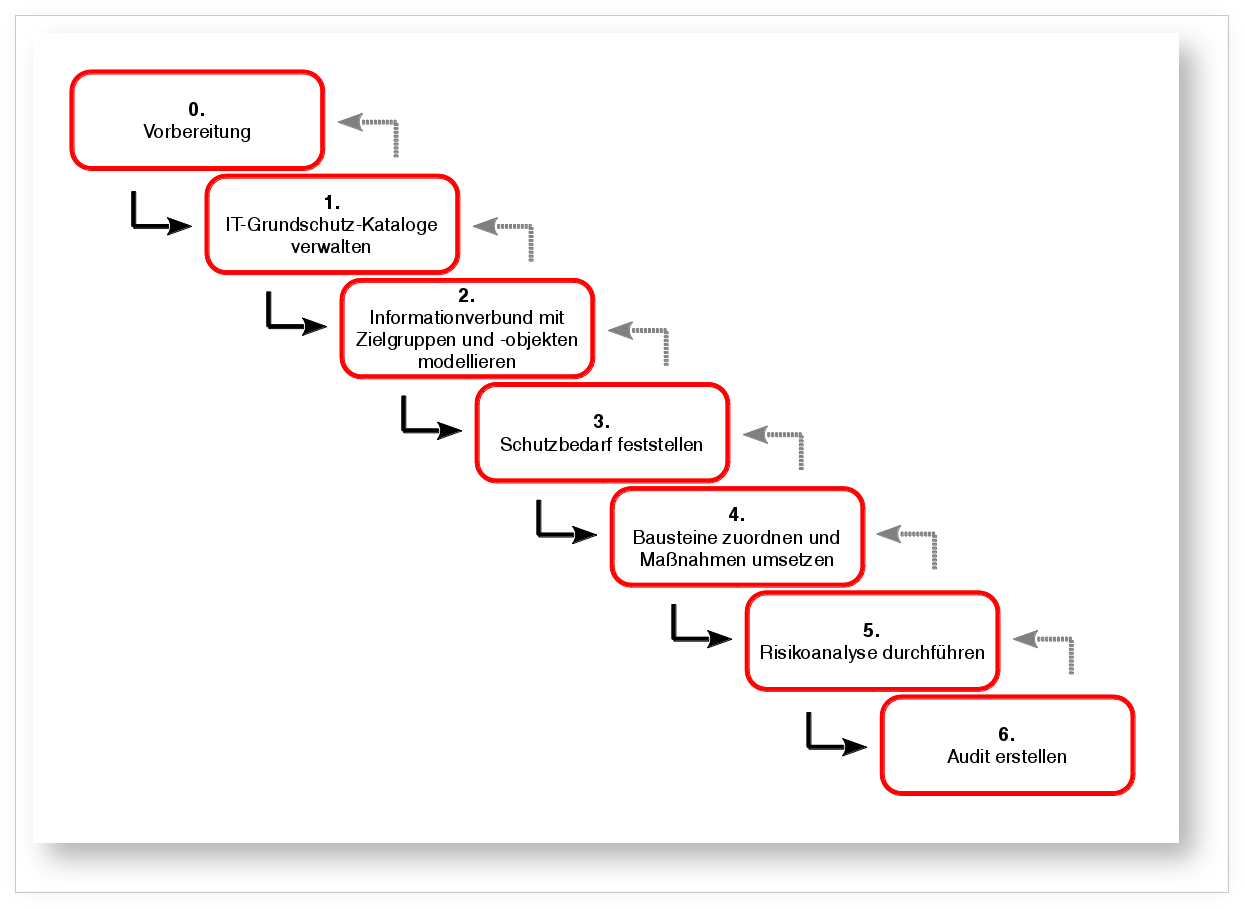
The goal of this workflow is to create a solid documentation base to later support an audit and certification according to ISO 27001 based on IT-Grundschutz.
- Preparing the VIVA installation: The IT documentation in i-doit contains objects (including location and software assignments as well as port connections, where possible) that are modeled into services and should be covered by IT-Grundschutz.
- Managing IT-Grundschutz catalogs
- Import IT-Grundschutz catalog EL 15 from 2016
- Customize modules, measures, and threats (optional)
- Model information domain with target groups and target objects
- Determine protection needs
- Assign modules and implement measures
- Perform risk analysis
- Create audit
- Review reports and if applicable repeat steps 2-5 until reports no longer yield unavoidably negative results
- Enter information for reference document A.0 and A.1
- Create audits
- Post-process output